We spend a lot of time online, whether it’s for work, entertainment, studies or staying connected with our loved ones. Cyber security is more important than ever, given that we’re turning into a world that relies largely on going digital.
In this article, we’ll look at what cyber security is, why it is crucial in the digital age, different types of cyber threats, and of course some practical measures to safeguard against them.
What is cyber security?
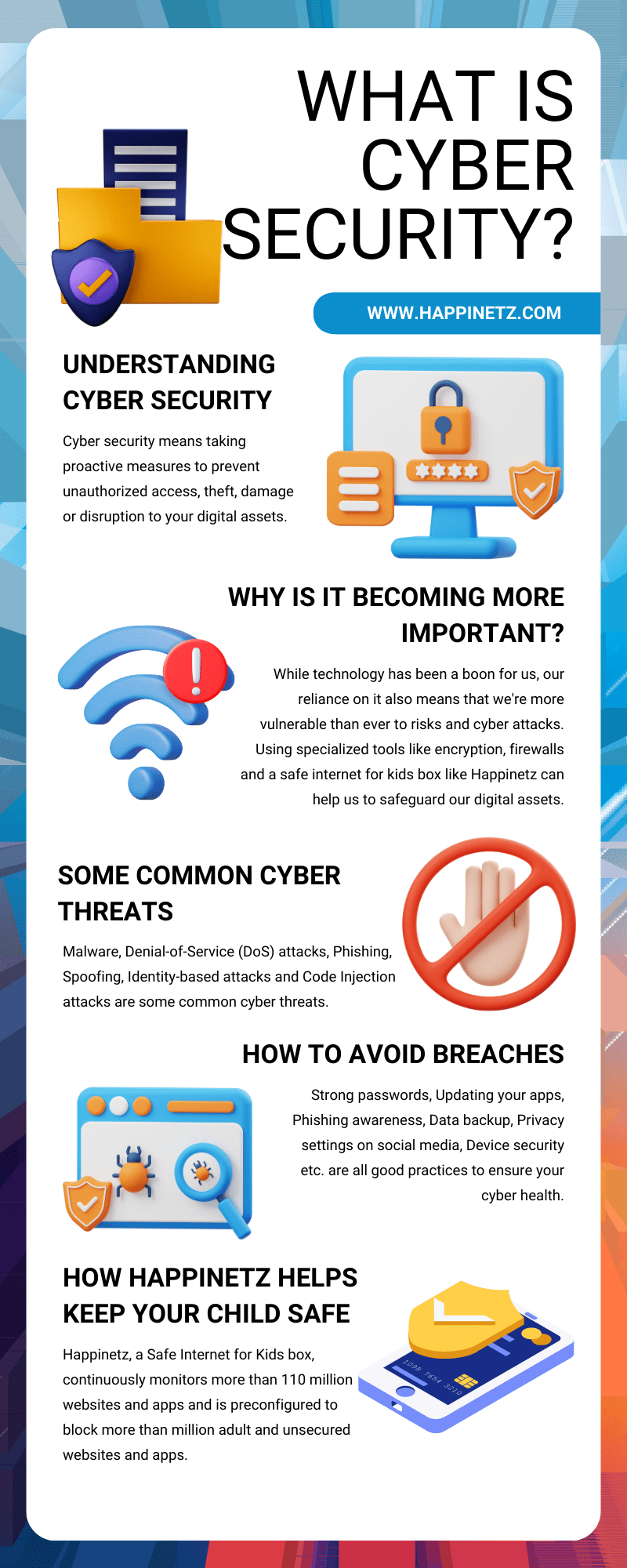
Cyber security simply refers to the proactive measures taken to safeguard computers, servers, mobile devices, electronic systems, networks, and data against malicious attacks. It is also commonly referred to as information technology security or electronic information security. The practice of cyber security involves defending these digital assets from unauthorized access, theft, damage, or disruption.
To put it simply, cyber security is like putting a lock on our digital devices and using special tools and techniques to keep our personal information safe from cyber criminals. By using cyber security, we make sure that our online activities and data are secure without worrying about what may go wrong.
Why is it becoming increasingly important in this digital age?
We are becoming increasingly reliant on digital technology these days. This has also escalated since the pandemic.
We cannot deny the fact that tech has made life easier. Not just smart phones, but now we have smart devices to do various tasks for us around the house and at work. Now children are born into tech too. Technology is introduced knowingly and unknowingly at a very young age. We have interactive games for children, older kids have classes online and rely on the internet to research their homework, learn different courses, stay in touch with friends and also for entertainment.
The digital age has brought us convenience and efficiency, but that comes with exposure to risks. By implementing robust cyber security measures we can ensure a secure digital environment and make the best of digital technology.
Understanding how cyber security works
Cyber security protects computer networks from cyber attacks and unauthorized access. It is done by trying to anticipate and defend against cyber threats, and responding to security breaches when they do happen.
How is this done? By taking steps to protect our computers, phones, and networks. We do this by using special tools like firewalls and encryption, which act like barriers and locks to keep bad guys out. We can also use secure coding practices and access controls to make sure only the right people can access our sensitive information. Cyber security solutions also help us by identifying and stopping risks like dangerous websites, fake emails, viruses, and other types of threats that can harm our devices and steal our information.
Some search engines don’t track your browsing history and thus don’t show personalised ads. However, they may still show you ads on the basis of your IP address and other factors. So keeping in mind the benefits and drawbacks, it’s important to use a combination of approaches to achieve the level of ad blocking and privacy protection you need.
Now let’s look at the different kinds of cyber threats
Types of cyber threats
These can come in various forms, each of them posing unique risks. But don’t worry. By being aware of these threats we can better understand what measures to take to stay protected. Some common cyber threats are:
- Malware:
Malware refers to malicious software designed to seep into and damage computer systems. It includes viruses, worms, ransomware, and spyware. Malware can be spread through infected email attachments, compromised websites, or malicious downloads.Criminals can convince children to download malware masquerading as games, something they might find hard to resist. Do not click on unknown links and files! - Denial-of-Service (DoS) Attacks:
In a DoS attack, cybercriminals crowd a target system or network with an overwhelming amount of traffic or requests, causing it to become inaccessible to legitimate users. This can disrupt services, and cause significant damage. Children may not directly be targeted by DoS attacks but we can if we aren’t careful and that indirectly has repercussions on children’s online experiences. - Phishing:
Phishing attacks involve tricking users into revealing sensitive information, such as passwords or credit card details, by impersonating trustworthy entities via email, text messages, or fraudulent websites. Cyber criminals can use sites popular with children to identify potential victims, and then promise prizes in return for credit card details for example. Haven’t we heard of so many ways this is happening nowadays? - Spoofing:
Spoofing simply involves forging information. This includes IP spoofing, where the attacker manipulates the source IP address of network packets to appear as if they come from a trusted source, or email spoofing, where the sender's address is forged to appear legit. Attackers can impersonate classmates, friends, even teachers or other trustworthy authority figures in children’s lives. Spoofing can also happen in social engineering attacks such as a spoofed phone call or message from a "parent" asking for personal information or financial assistance. - Identity-Based Attacks:
These attacks aim to compromise user credentials or impersonate people or organizations. They can involve guessing passwords through brute-force methods or using stolen username and password combinations from previous breaches to gain unauthorized access. If children or even us use weak passwords, or the same password across multiple platforms without two-factor authentication (an extra layer of security) identity-based attacks can happen. - Code Injection Attacks:
Code injection attacks happen when criminals insert harmful code into a computer program or system. By this they find weaknesses and get unauthorized access. Children are subject to this when they download files or unknown applications from untrusted sources, when they enter online chatting platforms that are vulnerable, etc. - Cyberbullying:
A 2018 survey of children’s online behavior found that approximately 60% of children who use social media have witnessed some form of bullying. Social media and online games are part of children’s playgrounds today and most cyber bullying happens there. It can happen in the form of trolling on social media, online chatting, or virtual attacks while gaming. - Falling for scams:
Oftentimes we must have come across scams such as announcements we’ve won a lottery, etc. Children may fall prey to different kinds of scams such as promises of free access to games that are chargeable or special access to exclusive features on their favourite game. - Digital footprints that can make a comeback:
As much as we’d like to think what’s deleted online is actually deleted, it may not always be the case. That is why we must be conscious of our digital footprints. Something as simple as a picture or an opinion posted online, giving away personal information on public spaces or strangers online can come back to cause problems. - IoT-Based Attacks:
The Internet of Things (IoT) describes the network of physical objects embedded with sensors, software to connect and exchange data with other devices and systems over the internet. A good example of such networks is smart home devices. They can be vulnerable to attacks. Cybercriminals can exploit weak security measures in these devices to gain unauthorized access and wreak havoc.
Many of these threats are faced by us and children while spending time online and proper cyber hygiene that includes cyber security in place are some of the best practices to stay safe.
Cyber hygiene we can follow to avoid breaches
Cyber hygiene means practices and habits we can adopt to maintain good cyber health and minimize the risk of the discussed cyber threats.
We definitely have to take proactive measures for proper cyber hygiene. Some of these include:
Strong passwords:
Creating and using strong, unique passwords for each online account and regularly updating them. Avoid using the same password across multiple social networks.
Software updates:
Keeping our devices’ softwares, antivirus and applications up-to-date can sometimes be difficult if we are not very tech savvy, but we can always take help and do the needful. Ignoring legit updates can make us prone to cyber attacks.
Phishing awareness:
Be cautious when opening email attachments, clicking on links, ads, etc especially when they are from sources you aren’t aware of. Don’t be quick in providing sensitive information without verifying the legitimacy of emails/websites.
Unsecured sites and public Wi-Fi networks:
It is best not to share sensitive information on unsecured websites or public Wi-Fi networks. Look for the padlock symbol and "https" in the URL to ensure a secure connection.
Don’t forget to backup your data:
Regularly backing up important files and data to ensure they can be recovered in case of loss is always a great idea that prevents unnecessary stress.
Privacy settings on social media:
Make sure you check your privacy settings on social media platforms to ensure personal information that you want to keep private remains private. Privacy settings can also help ensure interactions with strangers is limited.
Device security:
Security features like firewalls, antivirus software, and encryption protects devices from malware and unauthorized access.
Wi-fi security:
Using secure Wi-Fi networks and avoiding connecting to public or unsecured networks that may expose devices and data to potential threats is ideal. Here, the Happinetz System can do the job for you when it comes to protecting your children from cyber threats. Let’s see how
Happinetz: Your cyber security ally
Using Happinetz is hassle free and has only a simple two step installation process.
The Happinetz Box is a device that connects to your home router, wired or wirelessly to filter out age-inappropriate content.
With one app installed on your phone you can navigate your childrens’ screen time with a personalized screen time manager, filter out unwanted apps and websites with its multi-level protection system and manage up to 10 devices!
Cyber threats can sound very intimidating, and rightly so, they are. But with the right kind of filters you don’t need to worry about your children’s online activity.
The Happinetz System filters websites and apps by categorizing and clubbing them under 15 categories. By default, adult and unsecured websites and apps are blocked. Basically it acts like a guardian by sending all app and website requests from their devices to a central filtering system, which determines whether the requests should be permitted or denied.
It filters out age-inappropriate content and phishing attacks by tracking more than 110 million website domains across the internet- the perfect ally and addition to your cyber hygiene routine.
Make tech your friend
In today's digital life, cyber security and good cyber hygiene go hand in hand and play a significant role in safeguarding our children when they’re online.
We cannot deny children internet usage but we can definitely provide the right kind of guidance.
There’s so much we can do with tech when used the right way. Happinetz could definitely be your expert friend in taking care of your concerns when it comes to online safety of children. Why not try it today?
Some FAQs you might have
What is cyber security in simple words?
Cybersecurity is the practice of protecting systems, networks, and programs from digital attacks. These cyberattacks are usually aimed at accessing, changing, or destroying sensitive information; extorting money and more.
What exactly does cyber security do?
Cyber security is similar to having a good locking system at home and protecting your belongings in lockers, etc. In the digital world, it means taking steps to keep our computers, devices, and information safe from hackers and other criminals. Cyber security includes using strong passwords, being careful about what you click on online, and making sure your software is up to date. It basically means having software and other methods to keep your and your children’s online activity and data safe.
Why is cyber security important?
Good cyber security can protect your online identity, save you from financial losses, it helps maintain privacy, trust, and security in the digital world we spend a lot of our time in.
Who needs cyber security?
All of us who use the internet and devices such as laptops, desk tops, tabs and such need cyber security. Anyone can be subject to a cyber crime so it’s best to stay aware and safe and have a happy online experience with cyber security in place.
What is the role of parents in cyber security?
The role of parents in cyber security is to educate, guide, and protect their children in the online world. This involves teaching them about online safety, privacy, and responsible internet use, monitoring their online activities, and implementing necessary security measures to safeguard their devices and personal information.
What is online safety?
Online Safety is being aware of possible threats that you could encounter in the digital world. These could be security threats, protecting and managing your personal data, and avoiding harmful or illegal content.
Why is online safety important?
Most people store a lot of personal information online. If you don't protect your devices properly when you're online, it's possible that you can be subject to any kind of cyber crimes.
What are the basics of cyber security for children?
- Online safety such as not sharing personal information on public spaces or with strangers
- Think before posting content: Once something is shared, it can be difficult to remove or control who sees it.
- Using strong passwords and 2 factor authentication across social media channels.
- Importance of privacy settings on each social media platform is very important.
- Not clicking on random links or downloading attachments from emails they don’t the source of.
- And the most important: We should encourage children to talk to a trusted adult if they come across something or someone online that makes them uncomfortable.
Learning cyber hygiene takes a while and these things should ideally be regularly discussed with children. With time it becomes a habit and the online space can be friendly and welcoming.
How to use social media safely for children?
We can teach children to use social media safely by
- Proper privacy settings
- Reporting and blocking when needed
- Being kind and respectful in online interactions with others
- Creating strong passwords
- Accepting friend requests only from known people
- Thinking before sharing
- Reporting any suspicious behavior
- Proper screen time management
- Exposure to age-appropriate content only
The key is to encourage open communication and lead by example so children feel comfortable sharing their concerns and asking questions.
What are some common signs you have faced a cyber attack?
- Unusual login attempts
- Unauthorized lockouts- You’ve been locked out of your account even after entering correct passwords.
- Unusual system behaviour such as slow performance, frequent pop ups, error messages and frequent crashes.
- Unexplained data usage, unusually high network activity, or a sudden slowdown in internet speed.
- Files or documents mysteriously disappearing or modified.
- Programs, apps or any kind of software appearing on your devices that you haven’t installed.
- Suspicious emails or messages asking you to click on links, give OTPs, or download unknown attachments.
What is the first thing you should do if you believe you are experiencing a cyber incident?
Turn off the internet to prevent any further damage. Children should inform the parents who can then report the incident and take necessary action. You can reach out to the National Cyber Crime Reporting portal (Helpline Number -1930) to register any complaint about cyber crime. You can also contact the nearest police station to file your complaint.